Yes, Your Video Baby Monitor Can Be Hacked. No, You Don’t Have to Stop Using It

The scary stories about hackers hijacking video baby monitors are true. But IP cameras are still safe to use, provided you take some basic steps to improve your home network security.
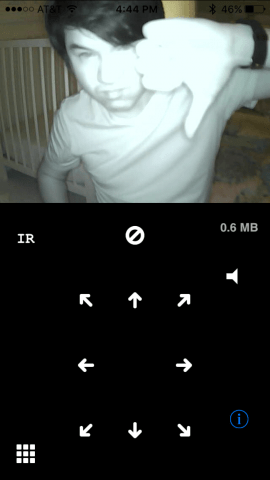
Video baby monitor hacking stories get lots of airplay on local news and instantly forwarded to me by my older relatives. What’s different about these stories is that the risks they identify are real.
These confirmed instances are chilling enough to make you want to run upstairs and unplug the baby monitor in your kid’s room right now. I almost did.
But after taking stock of the security measures I’d already put in place, I decided it was OK to keep using my baby monitors. The risks are real, but they are manageable.
Don’t get me wrong. I’m not immune to a little paranoia. For instance, I do have a Post-it covering the webcam on my laptop. (Seriously, when are they going to put little plastic shutters on these by default?). But my position on baby monitors is this:
Once you understand how hackers get into baby monitors and webcams, you can make a more informed decision on whether or not the security risks are worth the convenience. So, before you start warning all your friends and kids to stop using baby monitors, read through this post. Or better yet, forward them this one instead of the sensational story from your local news channel.
I have a problem with a lot of the way the media covers these stories. They are more clickbait than cautionary tales, and the advice they offer is cursory at best. The point of this post isn’t to shock and scare you—it’s to inform and prepare you.
How Hackers Access Baby Monitors: Dumb vs. Smart Monitors


The attack vector for older walkie-talkie/intercom type baby monitors (which I still use) is pretty simple. The dumb monitors are the radio equivalents of two tin cans on a string. All someone has to do is find the string and then put their can in the middle. That is, hijack the frequency and start playing death metal over it or something. There are two big limiting factors to the dumb monitor hack, though. The first is hardware. Right now, every kid over the age of 5 has a device that can use internet protocol (what smart baby monitors use). But to hijack a dumb baby monitor frequency, you’ll need to be somewhat handy with some gadgets you bought at RadioShack. The second factor is the range. You have to be pretty physically close to the baby monitor for it to work. For example, if I stand in my driveway with the receiver for my baby monitor, I’m too far away for the signal to work.
So, if someone starts hijacking your “dumb” baby monitor, go run out into the yard and find the little punk with the walkie-talkie who’s doing it and tell him you know where he lives, and you’re calling his parents.
That’s all old news.
Now, it’s not just older brothers and neighborhood kids pranking you. It’s the internet-connected video monitors and baby cameras that are making all the headlines lately. These are called internet protocol (IP) cameras because they use the internet and your local area network to communicate with your smartphone. The attack vector against these “smart” baby monitors is much broader. If a dumb baby monitor is two tin cans and a string, a smart baby cam is a tin can, and the string is the World Wide Web. Internet-connected baby monitors are potentially vulnerable to the full range of trolls, creeps, and criminals across the globe. And we all know that those people can be just absolutely reprehensible.
Internet Protocol Baby Monitor Security Issues
Every time I start talking about security with Steve, he starts doing his Shrek impersonation.
“Ogres Security measures are like onions.”
It’s all about the layers.


When it comes to your IP-enabled baby monitor, having just one stinky layer of insecurity can invite all the hackers. Then, your webcam could end up on some shady forum with links to hundreds of insecure webcams all across the globe. They exist. Don’t look for them if you value your soul.
At a very high level, here are the layers that apply to your video baby monitor. This comes from the fact that your video baby monitor works by connecting to your home wireless router, which I’m assuming is connected to the internet.
- Normal internet access to your router (Firewall protected)
- Video baby monitor access (Password protected, or better yet, disabled)
- Remote baby monitor access (Password protected, or better yet, disabled)
- Remote administrator access to your router (Password protected, or better yet, disabled)
- Video baby monitor access (Password protected)
- User/administrator local access to your router (Password protected)
- Wired (Password protected)
- Wireless (Password protected)
- Video baby monitor access (Password protected)
As you can see, in all cases, the attacker gets access to your baby monitor by first getting access to your router. So, the first and obvious layer of protection is to secure your wireless router. After that, there’s more you can do. But before we get into that, let me explain to you how the hackers can get in.
If you don’t care about all that, feel free to skip ahead to the Video Baby Monitor Security Checklist.
Compromising Your Router Security
When an attacker gets administrative access to your router, it’s pretty much game over for every device connected to it. Your baby monitor might be the least of your concerns. But to stay on topic, most baby monitors are configured by accessing their administrative “backstage” via your router. If a hacker gets access to your router, they can then start monkeying around with the security settings of your baby monitor.
Here’s how they can get in:
An attack via unauthorized internet access to your router is the least likely to occur. All routers use Network Address Translation (NAT) to filter out unauthorized incoming traffic. The only exception here is if you’ve purposefully gone in and enabled port forwarding or created a demilitarized zone. You’d usually only do this for programs like BitTorrent clients or high bandwidth online video games. If you don’t know what these are, ask your teenager if they did any of these things to your router. If not, you’re probably OK. You can check your router’s settings pages to make sure, though.
An attack via remote access to your router is similar. In the same way that you can set up your baby monitor to be legitimately accessed via the internet, you can have your router’s administration page accessible via a wide area network or the internet. This is instead of accessing your router’s configuration page by connecting to it directly via a wired or wireless connection. Unless you’re an IT administrator for a business, there’s practically no reason you need to do this—it just makes you more vulnerable. Go ahead and disable this feature on your router’s settings page. If you don’t ever remember enabling it, then it’s probably already disabled. It’ll usually be called something like “remote setup” or “Allow Setup over WAN.”


An attack via local access to your router is the same as remote access to your router, except a hacker will need to be within Wi-Fi range or able to plug directly into your router. This is rare, but don’t rule it out—think about open houses, parties, house sitters, etc. If you have an open wireless network, meaning anyone can connect without a password (why? why? why?), then your neighbor can get in as they please. Even if you have wireless passwords enabled, someone could plug into the router via an Ethernet connection, crack your router admin’s password (or use the factory default, if you haven’t changed it), and then go to town.
Compromising Your Baby Monitor Security
Let’s assume now that the hacker has access to your router and, therefore, your baby monitor’s configuration. Just like your router has default settings that protect it from unauthorized traffic, your baby monitor will usually have these protections in place out-of-the-box. But many video baby monitors also have UPnP and port forwarding settings that can be enabled to make the camera less secure.
Also, if you haven’t set a password for your baby monitor or changed the factory default password, someone can easily access the camera now that they have router access. They can continue using the known factory default password or put it in their backdoor account.


Until now, we’ve been dealing with unauthorized access to your router via the internet. A lot of these smart baby monitors enable you to access your baby monitor via the internet legitimately. That is, say you’re at work or on a date or something, and you want to look at your little sleeping angel from your phone. This is a feature you can enable from within the video baby camera’s software settings. But I don’t think you should. The bandwidth and security implications of enabling this feature are too great if you don’t know what you’re doing. So save yourself the risk and don’t use your video baby monitor as a nanny cam. Just text your babysitter and ask how things are going, okay?
The problem with enabling Internet access to your baby monitor vastly simplifies the hacker’s work. Instead of penetrating your router, gaining administrative access to your router, and then administrative access to your baby monitor, they have to crack the password you set for remote access to your baby monitor. It’s a bit like leaving a key under the doormat by your front door. If it’s easy and convenient for you to access, it’s easy and convenient for hackers to access.
Video Baby Monitor Security Non-issues
So, all that should give you a good idea of how hackers can get into your baby monitor. It’s pretty much simple home wireless network security stuff. There isn’t anything inherently dangerous about baby monitors that aren’t true for all the devices on your home network. The difference is that the temptation to prank maliciously is much higher, and the creep factor is extra high. If you treat your baby monitor with the same vigilance as your phone, laptop, and tablet, you should be OK.
Simply having a video baby monitor in the house doesn’t immediately open up a window to the world. Plus, you don’t have to worry about someone intercepting the digital video signal over the air. Digital video baby monitors use encrypted signals. It’d be way too hard for someone to crack these, and they’d need to be within signal range.
Video Baby Monitor Security Checklist
Whether or not you read all the slightly technical mumbo jumbo I just wrote, there are some pretty simple steps you can take to make your video baby monitor secure. Do them one at a time, and if you need help with your particular baby monitor model or router model, check the manufacturer’s documentation or leave a comment. If you leave a comment, make sure you get your question answered before connecting your device.

- Secure your wireless router. I could write an entire post on this. But fortunately, Andre already did, so I don’t have to: Secure Your Wi-Fi Router Now With These Security Tips. Along those lines:
- Update the firmware for your router.
- Disable remote access to your router. Don’t let it be configured from anywhere but right inside your house, connected to the wireless or wired network.
- Set a password for your baby monitor, if you haven’t already (why? why? why?). You should also make sure you have a strong password.
- Change or remove the default login. Some cameras and routers have default login information, something stupid like “root” as the user and “password” for the password. Even if you’ve set up your login information, you should ensure that the old default login credentials have been removed or changed.
- Update the firmware for your camera. The steps for doing this are different for every manufacturer. Shoot me a message if you need help.
- Disable DDNS on your camera if it has it.
- Disable port forwarding or UPnP on your camera if it has it.
- Disable remote access to your baby camera. It’s convenient but unnecessary. And if you don’t have an unlimited data plan, it’s going to be expensive, too. Sending video feeds over the internet to a phone eats up a lot of data. If you are adamant about using remote access to your camera, make sure you do the following as well:
- Change the port that’s used to access your camera. The default is 80, and that’s the one that hackers will check first. Change it to something above 8100, if you can.
- Periodically check the logs for unauthorized access. When looking at your log, look for unusual things, like IP addresses you don’t recognize or strange access times (1 PM when you weren’t even home, for example).
If you address all the items above, you should have protected all the typical attack vectors to the best of your ability.
Did I miss anything? Let me—and your fellow groovyPost readers—know in the comments section.
11 Comments
Leave a Reply
Leave a Reply







Dave
September 27, 2016 at 12:42 pm
That’s a really useful guide for securing things – a lot of people assume that it’s the baby monitor itself that’s insecure, when all too often the weak link is the home wifi itself as you point out. After all, people should be taking their home network more seriously in the first place, no doubt they’re logging into their internet banking on it, and giving away all sorts of personal information.
Jenny
March 24, 2017 at 2:27 am
I have an old summer baby monitor, my boy turn 6 months today, he’s been sleeping in his crib for over a month now. I just woke up to my son playing in his crib and realized someone was zooming in and out on him. I freaked out, I gave him the finger and turned it off. Mine doesn’t even have the fonction for wifi and they still hacked it
Greg
July 17, 2017 at 7:55 am
Are you sure that wasn’t just the camera autofocusing?
JM
April 23, 2018 at 9:33 pm
I also have a Summer Infant monitor, I could’ve sworn tonight I heard someone say hi over it. It is just a camera and video monitor, no WiFi involved. Can they hear or see my child? I feel sick about this.
Kimberly
January 25, 2020 at 8:50 pm
I just had a similar situation. I’m using a Lorex video monitor that is now about 7 years old. I did try out the option to connect it to the computer I had a the time time. However, I haven’t used that feature i years and I don’t have it connected to my current computer or wifi. I believe it had me set up a skype account for the feed. I have always attempted to be aware that hacking is possible so I have done my best to make sure there was nothing more interesting than sleeping children was visible (though there have been moments where I forgot the camera was on).
I always assumed that, if it was hacked, they would not have full function, just able to see/hear what I see, and that it could only be hacked by someone in close proximity (bringing down the risk down). However, tonight, I took an extra precaution of making sure the camera couldn’t actually view my kids. Just before I planned to go to bed, I checked on my kids and the camera started moving. Maybe It malfunctioned but, well, now I’ve unplugged the monitor, I’m wide awake, laying next to them and googling baby monitors being hacked. :|
Kp
August 2, 2017 at 2:34 pm
So I’m looking at the part where you say digital video monitors are much harder to hack. Would it be safest then to just get one of these?
Caren
September 9, 2017 at 7:13 pm
I bought a second hand camera. It’s the summer split screen camera. How do I know what was required during setup or isn’t even a camera that requires internet connection.
Alice
September 20, 2017 at 1:28 pm
The key is to ensure the wifi at home is really secure and there shouldnt be too many issues surely? I can imagine that the hacking of a monitor is a very rare occurance?
Jennifer
December 4, 2020 at 6:52 am
I followed it. It’s really amazing and good to apply. I subscribe to it for my relatives.
secure video baby monitor
Becass
December 21, 2020 at 10:56 am
I have an arlo monitor that syncs with other home cameras. It connects through my password protected wifi and I pull it up, with a password, on my phone, which 2 factors to text me a code. So, the monitor can be viewed, as you say, on a date, but it needs a 2 factor authentication to view it, in or out of the house.
Safe? Not safe? More access points?
Daniel Tristan
August 26, 2021 at 9:02 am
Hey, I think you missed an important point. I am a software engineer and I work from home, so trust me, my network is secure and has many layers that will make it very difficult for someone to hack into my network.
The real problem here are the companies in which they have hosted their monitors, for example, yesterday, at 4 in the morning someone haked the camera that is in my son room and he started talking to my baby in French, (I lived in France for a year and in Montreal for three years and clearly that guy had a pretty good French accent)
That guy did not hack my network, he hacked the Hubble application and with that information he had access to all my cameras, I think the most important thing is the security and infrastructure that a monitor company has, I am going to change all my cameras with Arlo systems and see how it goes.
Wish me luck