10 Step Security Guide for Keeping your Computer Virus Free

groovyPost 10 Step Security Guide to Keeping your Computer Virus Free and Your Data Safe!
I’ve managed to dodge the bullet of virus and malware infection on all my numerous devices for more than 30 years of using various computers daily. How did I achieve this feat? By almost religiously following the 10-Step Security Guide I’ve outlined below. Sounds simple, right?
The Big Reveal? What’s in this Security Guide? The strategy is straightforward — I stick to a set of basic principles when operating my computers and lean heavily on sound judgment (or what you might call common sense) when something seems off.
So far, this approach has served me well, and if you’re curious about partaking in this streak of digital well-being, have a glance at my (maybe not so) concise guide to computer security below. Who knows, it might just carry you through the next ten years without a scratch from viruses. ;)
Diving Into My Cybersecurity Soliloquy …
I’d like to begin by sharing a core belief that I apply across all my tech gadgets: there’s no magic wand in the realm of information security. Achieving Information Security, or computer security as some prefer to call it, isn’t as simple as a one-and-done action. It’s about a commitment to a series of actions now, tomorrow, next week, and for as long as you’re using a computing device.
Moreover, robust Information Security involves building multiple layers of defense. Each additional layer fortifies your digital “fortress,” making it increasingly challenging for bad actors to penetrate. The more security layers you have, the better your chances of maintaining a pristine and secure system from the nefarious reaches of malware.
Hence, the security steps I’ve laid out below are not ranked in any specific order. Each one represents an additional layer in your comprehensive security strategy. Individually, they leave you vulnerable, but together, they forge a formidable barrier safeguarding your data against the malevolent elements of the digital world.
1. Install Operating System Security Updates
Windows, macOS, Linux, etc. Despite their differences, all operating systems have one thing in common: they inherently have flaws/bugs/issues/etc. I don’t know, maybe this comes as a surprise to you, but humans are far from perfect, and all of these operating systems are written by humans.
That’s the main reason OS updates are released: the developers find new bugs and exploits, and issue patches to plug those holes in your information security. That’s why you must make sure your computer stays protected by installing the latest security updates.
If you’re an Apple user I can see your smirk from here because you think Macs don’t have any security issues right? Think again — SecurityWeek noted that a total of 21 new malware families emerged in 2023 targeting macOS-based computers. That marked an increase of more than 50% compared to 2022. Even Apple points out the need for antivirus protection in macOS.
2. Install Application Security Updates
Similar to #1, the software you install on your computer is flawed the moment it’s written. In other words, the minute you install a new app on your computer, your computer becomes that much less secure. To make things worse, small software companies don’t have the massive security budgets larger corporations have, like Microsoft and Apple, so it’s not uncommon for “security” to be left out entirely.
The bad guys (hackers) know this, so rather than try to break Microsoft, many are targeting the software on your computer. What makes this even easier for hackers is the fact that they can count on a few pieces of software installed on just about every computer out there.
You guessed it, that’s Adobe Acrobat Reader. Unfortunately for us, Adobe doesn’t have the greatest track record for writing secure software.
The moral of the story is to make sure you’re running the latest versions of software on your system and verify at least once a month that you’ve installed the latest security updates as well. This is not easy if the software doesn’t have an auto-update feature. Nevertheless, that’s a massive attack surface that needs to be kept clean. Yes, this is a tough one, and it will take a lot of work. Good luck, groovyReaders!
3. Install a Quality Anti-Malware Application
With so many high-quality free antivirus applications available for most operating systems, you have no excuse to be running with no antivirus software. My recommendation? Keep things simple and use Microsoft’s free antivirus client. If you’re not a Microsoft Windows user, we’ve got a list of great options for the Mac. By running anti-malware AV software, you’re not just protecting yourself, you’re also protecting the community.
4. Keep Your Antivirus Application Updated with the Latest Virus Signatures
New viruses and malware strains spread like wildfire across the internet every day. To keep pace with these threats, antivirus firms continuously refine their software, enabling it to recognize and thwart (with any luck) the intrusion of these harmful programs into your system. These are known as either “signatures” or “definitions,” depending on the software you’re using.
In the past, refreshing your computer with the latest AV definitions weekly or monthly was good enough. However, given the relentless evolution of cyber threats nowadays, it’s imperative to update your AV software as frequently as possible, daily or even hourly. This makes sure your system is armored against the freshest dangers lurking online.
Windows Defender doesn’t allow for hourly updates (unless you’re inclined to employ a batch script to manually initiate updates — a strategy I wouldn’t endorse). Nevertheless, you can configure it to automatically update itself every day. That should suffice for robust protection.


For users of other AV solutions like McAfee, verifying that you’re equipped with the latest signatures is straightforward. Usually, it’s as easy as right-clicking the program’s icon in your system tray and selecting About. You might even find options within your AV software to schedule updates and refreshes of its definitions and signatures at intervals ranging from weekly to daily, hourly, or even every minute (though I wouldn’t advise the latter).
Let’s be clear: if not regularly updated, your antivirus software becomes useless 2 to 3 weeks after you install it, sometimes the day of installation. Consider this simile: your antivirus is like a firearm, and the security signature updates dispensed daily are its ammunition. A gun without ammo is worthless. Similarly, an antivirus without continuous updates to its signature database is ineffective. Therefore, it’s critical to keep it refreshed daily with the newest signatures and definitions.
5. Install a good Anti-Spyware / Adware / Malware application
Some might argue that if you have a good AV application installed, you don’t need to worry about installing a specific Anti-Spyware / Adware application. To me, it’s a lot like going out in the bitter cold. You’re always best to dress in layers to protect yourself. I believe computer security is best handled the same way, with layers of security. You’ll notice that Microsoft’s built-in security protection for Windows takes that approach.
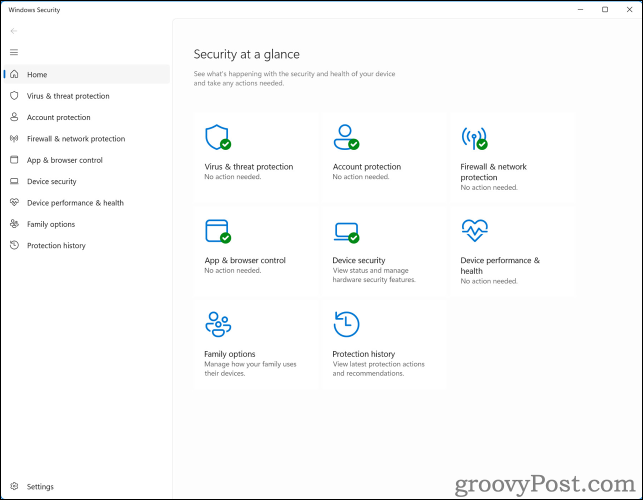
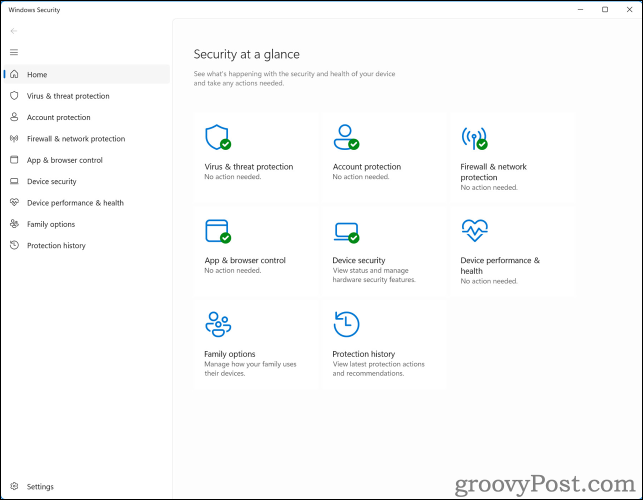
That way, if a layer misses an exploit due to an old virus signature, the next layer might get it. So, with that in mind, I like to install an anti-spyware application along with an antivirus application just for the added layer of security.
Despite all the negative press from the Vista days due to performance issues… Windows Defender has worked well on all of my Windows systems with little to no impact on system performance.
Another good option if you want a different set of signature files between your antivirus app and your anti-spyware app is Malwarebytes. They have both been around for years and are very widely used across the world. It’s probably my #2 choice, depending on my mood. ;)
6. Don’t be an Internet Victim! Use Your Brain!
Now that you’ve completed steps 1 through 5 above, guess what? You’re ready to open your web browser, surf the internet, and use email! Just don’t get all carried away with the feeling of invincibility, thinking your PC is fully updated.
The following few tips are actually the most important. That’s right …. If you ignore a few tips below, your computer will probably end up infected with malicious software in just a matter of weeks, if not days.
7. Use Common Sense While Using Email
Although many scams have moved to text messages and phone calls, email is still a very popular tool used by evil people all around the planet. Unfortunately, even in 2024, it’s still an extremely effective way to hook people using social engineering. With that in mind, here are just a few examples of things to look out for.
- If you get an email from someone you don’t know, DELETE IT!
- Did you receive an email with a file attachment you weren’t expecting, even from a close friend or family member? DELETE IT! If the email was legit, ask them about it later and have them resend it.
- If a bank or credit card company emails you to tell you your account was hacked, DELETE IT! Banks will ALWAYS call or text you if there is a problem with your account. I guarantee this 100% of the time. Even if the email is legit, DELETE IT and call your bank. You don’t want all those private details in email anyway.
- If you get an email that tells you to send money somewhere, DELETE IT!
- If you get an email that tells you that you’ve won money … DELETE IT!
- If you get an email with an attachment that’s compressed and password-protected, DELETE IT!
- Be wary of poorly written, broken English emails. For one, it’s not worth reading, and two, it’s probably a scam or a virus.
- Be very wary of Greeting cards and e-vites. Most of them want you to click on a link.
- If you get an email from your mother-in-law telling you about a new virus on the internet, DELETE IT (sorry, I couldn’t resist).
- Bonus tip (since I wanted to list 10). Although not an email, if someone calls you on the phone and tells you they are the US Government, FBI, IRS, a Bank or Microsoft, etc., you should briefly get their name and company they are calling from, then hang up on them. You can then call them back using an official number from the company/gov website. A simple scam is impersonating law enforcement or a tech support company to tell you you’ve been hacked or going to jail if you don’t install software on your computer so they can help you. Don’t fall for it. Hang up.
Remember – If something doesn’t look right or if an email scares you … DELETE IT. When in doubt, throw it out!
8. Surf the Web Securely
If you visit a website that offers to scan your computer for viruses, leave the site immediately. It’s probably a scam to get you to install malware on your computer. Whatever you do, NEVER install software from a website unless you know exactly what the software is and go to that site to install it.
Some websites will prompt you to install software to either scan your computer for malicious software or to allow you to watch a movie or just use the site. Be VERY wary of this stuff. You can’t know what’s getting installed. Just keep in mind that no credible, modern company will ask you to install anything to view their site.
Never install free games found on the internet. If you want a game for your kids, stick to games you can find on the Microsoft Store or Mac App Store. If a kids’ site wants you to install something on your computer, forget it. Run away!
Ready for this one? If you can … avoid the shadowy side of the internet. That’s right, I’m talking about porn sites, hacking sites, and BitTorrent sites. The same goes for those password sites for porn and applications. These are all FULL of malicious software that is just waiting to be installed on your computer.
Don’t steal software by downloading it from BitTorrent sites. Almost 100% of the time, the software you download from a torrent will be protected by copyright law and is probably infected with some malicious code/virus that will install right alongside the application. Best to just buy the software you want and stay away from the “Free / Illegal” side of the internet.
9. Use a Unique, Strong Password and Two-Factor Authentication For Each of Your Online Accounts
Password management is key to keeping your computer and your online data secure. Honestly, in 2024, you really shouldn’t be coming up with a password at all. Instead, you should use a password manager like 1Password, which is my favorite. It will create and store passwords for you, and when you visit a website, it will automatcilly enter in the Username and PW for that website.
Personally, I only know a single password for every website I use daily. The password is my “Master Password” that gets me into 1Password. This is where all my passwords are stored.
If you must create a password, however, please follow the three steps below to help you create a secure and unique password!
- A strong password is a unique password. As tempting as it might be, never use the same password on multiple websites. Sharing passwords between sites is like Russian Roulette. All it takes is one website hack to ruin your day. Add a layer of security to your online accounts by using unique passwords.
- Don’t use dictionary words. Yeah, I know, your kids are adorable, but their names make horrible passwords, as do months of the year. Dictionary words are easy to guess, and there are about a million apps out there that specialize in attacking accounts using dictionary words in all known languages.
- Use a passphrase. Do you mean like an actual phrase? Yes, that’s exactly what I mean. The great thing about a passphrase is it’s long, it’s not a dictionary word and in some cases, it’s easy to include special characters. Unfortunately, Twitter doesn’t allow spaces in their passwords but you can still use special characters like in my example: ilovegroovypostsoverymuch!!
Wow, a 27-character password that is easy to remember and includes two special characters. Good luck trying to hack a password like that one!
You should also take advantage of two-factor authentication whenever possible. This is a fantastic way to add one more layer of security to your online accounts. Many popular online services support 2FA, including Google, Apple, Facebook, Twitter, Dropbox, and more. If you don’t understand what 2FA is and I just confused you, jump over to my free Tech Support Forum and post your question there. No, it’s not a scam site. It’s just easier to answer questions and walk you through 2FA on that site.
10. Routine System Maintenance
Backup … oh … how could we forget about backups? No matter how many precautions you take, having a solid and reliable backup is a must-have. If you’re not backing up your system today, stop what you’re doing and take the steps necessary to get a full system backup now! What should you use? There are a million different options. If you prefer to keep your backup close, grab a USB drive and create a system image.
If you want my advice, use Backblaze. It’s a rock-solid cloud solution that just works. Period. It’s cost-effective for both a single PC and all the PCs in your home (Windows or Mac). I loved it so much, I bought it for all my computers at home AND for work. Yup, we run over 2000 copies of Crashplan at my corporation, and it works great!
As a final security tip, you should routinely clean out the cobwebs on your system by deleting old cookies, Internet history, browser cache, and system temp folders. I’ve already written a guide for this using a free tool called CCleaner. That said, the tool is very simple to use, automatically updates itself and if you follow my guide — is safe to use.
This final tip is important because as you surf the web and install software, you pick up “things” like small bits of websites in your cache as well as cookies that track your surfing, etc. By clearing out these small bits from time to time, you’re not only wiping away those tracking cookies, but you’re also protecting yourself in the event your system becomes compromised. Granted, if that happens, you’re probably already in trouble. However, as I mentioned above, security is about layers, and this is just one more you can add to your routine.
Conclusion
It’s important to note that this Security Guide is not a 100% comprehensive list. Honestly, with Information Security, nothing is 100%. As already stated, it’s about doing a lot of little things and using common sense vs. finding an end-all security guide on the internet somewhere. That being said, if you notice something obvious that I missed, please contribute and drop your tips in the comments below, and I’ll do my best to quickly add it to the Security Guide. I’m sure all the groovyReaders out there will appreciate it!
This article received a significant update on 3/6/2024. Original publish date: 2/18/2010.
22 Comments
Leave a Reply
Leave a Reply







Kalyan
February 18, 2010 at 6:38 am
Excellent collection. I had most of these in my head, but thanks for bundling all of these for me.
I can advise a few more.. maybe you will find them useful to add..
1. Staying away from free browser toolbars
2. Don’t use external Hard disks and USB sticks without scanning them if they have been to other computers
3. Enable phishing protection in browsers
4. Check Urls when entering username/password on a website after clicking a link in email.
shockersh
February 18, 2010 at 8:43 am
@ Kalyan – Yeah those are great additions.
#2 just happened to me. A few months ago Information security stopped by my desk at work because they said I was full of virus infected crap on my box. Turns out it was the External USB drive I connected to my PC at work. The external drive was from my Sisters PC. She gave it to me so I could grab all her family photo’s and put them up on a website. Turns out it was just FULL of malware. So yeah, lesson learned!!!
#4 – Another good one. It’s also good to check the URL from an email and verify the ROOT of the domain is really what you think of it.
In other words, I get emails all the time that say:
Your account has been hacked. Click here to confirm it’s not you and the link is:
Steve Krause
February 19, 2010 at 9:34 am
Great feedback Kalyan. Couldn’t agree more with each bullet you laid out. I think #1 is a one worth consideration. Toolbars are a big privacy black hole. I’m going to bet each of the EULA for them are quite scary. #4 also can be nasty if your not paying attention to the phishing schemes…
shockersh
February 18, 2010 at 8:38 am
Great list.
So many people do a great job protecting their OS with regular patches but forget to patch the applications on their PC…… so good call out.
I think you should also add something about use CCLeaner or some other tool to regularly wipe crap off your boxes temp files etc… Then again, I guess that’s more of a privacy thing and not really “Security” protection related.
Anyway, good list.
MrGroove
August 22, 2011 at 9:39 am
Added! Good Reminder!
mechBgon
November 13, 2010 at 7:03 pm
I also suggest the new EMET 2.0 utility from Microsoft. It makes it simple to fully enable hardware-level Data Execution Prevention and SEHOP, and you can also add extra mitigations to any apps you think would be likely targets (browsers, media players, IM and VoIP programs, PDF readers, Java, and so forth). Free, pretty straightforward.
A couple others:
1) make a separate Admin-level user account, then switch your “daily-driver” users (including yourself) to Standard User accounts. Bust out the Admin account when you actually need it, lay it aside when you don’t.
2) run the Secunia PSI checkup from secunia.com at least every couple weeks. It’s free for home users, and makes it really easy to tell if you need to patch some of your applications.
3) if your computer has users who don’t always recognize good from bad, you can enable Parental Controls to arbitrarily prevent them from executing files that you didn’t put on the system and pre-approve. It’s not without its drawbacks, but it’s a lot easier to deal with than a six-hour adventure in rootkit removal would be :) For the full-strength version, called Software Restriction Policy, you need the Business/Pro/Ultimate/Enterprise levels of Windows.
Chooibah
August 16, 2011 at 5:07 pm
Separate admin account, this in my opinion is one of the most important security layers available. Even on Windows 7 with UAC I use a locked down account and escalate only when needed (99% prompted for credentials when needed) as you never know whether UAC under an admin account will be circumvented (again).
For non-technical users, education is key, I always try to explain that if you are prompted to allow something then make sure you know what it is and that you wanted to run it.
I’m sure there are statistics from a study stating that at least 70-80% of malicious code would be prevented from running successfully without admin privileges… unfortunately I can’t find the link so don’t quote me on the figures! The closest I can find is http://www.zimbio.com/Windows+XP/articles/hlE1vpb4500/Configure+Admin+Rights+More+Secure+Windows which states “The key finding shows that 90 percent of critical Windows 7 vulnerabilities could be mitigated simply by not allowing standard users to run with administrator privileges” but I cannot confirm the reputability of the source (beyondtrust.com)
MrGroove
August 22, 2011 at 3:41 pm
Thanks for the tips @Chooibah – and yeah I agree. Running with least privilege is another great way to lower the attack surface. I primarily didn’t mention it because frankly, I’ve found it really really hard to convince people to not run email and their browser while logged in with admin rights. This probably deserves its very own groovyPost.
None
August 22, 2011 at 2:46 am
Not a bad article about security and preventing the obvious, however it was extremely difficult to read. My 4th grade godson has better grammar. When YOU’RE going to put something for everyone to read then maybe YOUR writing should be correct. Understand the concept between your and you’re?
Steve
August 22, 2011 at 3:42 pm
Hi @none – That is your name right? Thanks for the feedback (honestly). I did have a few oops in there. If you can see any I missed, drop another note.
-S
Charles C
November 1, 2011 at 5:57 pm
Steve, never had a virus? I would beleive you if you said you got one, but caught it with AV as it was loading. Anyway, I have a couple of items, #2 mostly that I have listed as a quick hit list. Thanks for the info.
Roibert Brode
May 25, 2012 at 12:37 pm
A wonderful article full of great information and with the exception of one post regarding your grammar, some great informative responses. Thank you.
Steve Krause
March 6, 2024 at 12:27 pm
Thanks for the feedback Robert. I’m glad you enjoyed the article. I keep it updated so be sure to check back later for new tips.
Icd-T
July 5, 2012 at 10:41 am
Well, I am going to go change all my passwords, which are all the same in some way, shape or form. Because of reading previous articles of yours, I have Just Cloud back up, and a malware dystroyer…Love your articles, I have learned so much!
Steve Krause
September 6, 2012 at 9:53 pm
Thanks for the feedback! It means a lot coming from a reader.
I always say its better to be proactive vs reactive. Change your pw today! :)
Chris
September 6, 2012 at 12:39 pm
How about Norton Ghost for Back Up.
Steve Krause
September 6, 2012 at 12:55 pm
Great application but a little on the geeky side for most people. Plus, it stores the backup local which is bad if your PC is stolen or your house burns down…. Probably better to go cloud with Crashplan or Carbonite. That being said, any backup is better than NO backup!
Chris
September 6, 2012 at 12:53 pm
Could I install SpyBot Search and Destroy and run it Occasionally and not use it All the time with MSE and Kaspersky.
Steve Krause
September 6, 2012 at 9:59 pm
Spybot search and destroy is a great app. I uses to install it in all my systems and my customers systems.
Not really sure why I stopped using it. I think over the years my confidence has grown more and more with Microsoft Security Essentials.
Spybot is still a great app. I know a lot of ppl still use it so yeah, nothing wrong with keeping it on your system.
Do you also keep TeaTimer installed with it?
Chris
March 10, 2024 at 4:55 pm
How about a VPN.
Steve Krause
March 12, 2024 at 1:47 pm
Good question Chris.
Using VPN on your mobile phone and computer is important yes. Anytime I use a Wi-Fi network which is NOT at my home and I can’t use my mobile to tether, I’ll use my VPN. 100% no exception. I prefer Private Internet Access however, NordVPN is also good. I’ve used several but prefer PIA.
Steve Krause
March 26, 2024 at 3:52 pm
It’s been a few years, but I decided it needed a fresh coat of paint on this article.
If you see anything we missed, let me know.
Steve
groovyPost