How Safe is it to Download Chrome Extensions?
Google Chrome extensions are popping up faster than you can say, “There’s an app for that.” As a result, the Google Security team can’t keep up with inspecting every single one of them. There are a lot of great, useful extensions for Chrome, but there are also some bad apples in the bunch that pose a real threat to privacy. Wondering exactly how safe you are with Chrome extensions? I was, so I did some research.
As it stands, this is the biggest thing that turns me off of Chrome extensions. I know it isn’t any better than what other browsers offer, but I thought they might be a little more strict with the new Chrome Web Store. Google doesn’t have a set privacy policy or terms of service regarding extensions made by third parties, so they can do whatever they want with whatever data they collect. Regarding this, Google has said:
If you install an extension on Google Chrome, it can store data locally and send any data it has permission to access to any third party server that it has permission to communicate with. Therefore you should be very careful that you know and trust the developer of the extension…
…If you install a plug-in on Google Chrome, any data processed by the plug-in will be handled in accordance with the policies of the developer of the plug-in.
For example, there is a developer spammer for a duped-up DropBox extension, and they are marked as a “verified author.” but their website is almost completely blank, and they don’t have any policies or terms of service of their own. On top of that, the permissions it is asking for are still rather vague;
- Your data on *.dropbox.com
- Your tabs and browsing activity
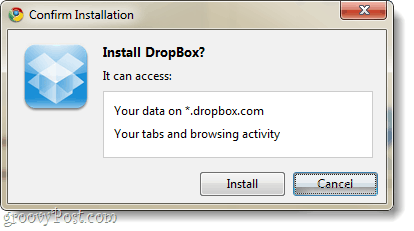
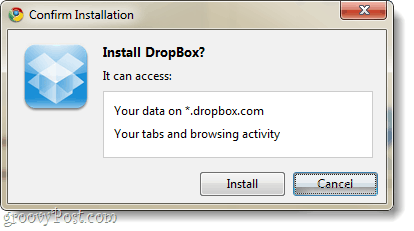
Browsing history and tabs could mean that this extension gives data on every single site you open in your browser, and access to Dropbox.com may let the extension have access to all of your Dropbox files. The other Dropbox apps that it likely copied don’t require permission to access your tabs and browsing activity. The Google code site delves into this in further detail, and the last update on the matter came from Googler Tony in July of 2010 -where he said:
Depending on the extension you install, the extension might need legitimate access to various things to carry out its purpose. However, this same ability means the extension can have the ability to read information submitted on the page, which includes private data. This is not to say it’s going to do this or do something malicious with it, but it *can* if the extension author is ill-intentioned and built his extension specifically for this purpose. This is why we always advise users to only download extensions from authors they know and trust (they have great reviews, have a lot of users, good reputation, etc).
Got it -don’t download apps from shady developers. But what about the “verified” author tag?


What does it mean if a Chrome extensions developer is “verified?”
In August 2010, Google started requiring a one-time $5 fee to sign up for the Chrome Extensions Gallery. Their intention in doing this was to prevent spam and cut down on the number of malicious extensions added to the gallery. It’s successfully reduced the amount of fraud, but it doesn’t stop someone from just paying $5 and uploading an information-stealing app. Of course, fraudulent apps don’t tend to last very long since users cannot report them.
Conclusion
You need to be smart about downloading extensions. The Google Chrome Extensions Gallery is filled with mostly well-intentioned developers. But all it takes is one bad guy to steal all of your internet browsing data, so pay attention to extension reviews, the number of users, and who the developer actually is. The overall lesson is still: if you don’t trust the developer, don’t install their extension.
1 Comment
Leave a Reply
Leave a Reply







patricia lane
February 2, 2023 at 6:55 pm
apparently, if you go to settings, autofill, password manager, then you can export your passwords as a csv. then import into the new chrome installation